Students at the University of Manchester are facing a heavy threat as the ransomware operation responsible for a recent cyberattack has initiated contact. In a turn of events, the hackers have started sending emails to students, revealing their intentions to leak stolen data due to the university's failure to meet their extortion demands.
The malicious actors claim to have successfully exfiltrated an astounding 7 TB of data during the cyberattack that transpired on June 6th. This development came to light when the contents of the hackers' email were shared with amplifying concerns about the impending data breach and its potential consequences.
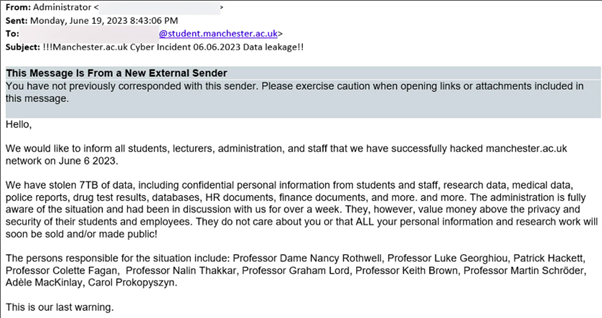
The email reads, “We would like to inform all students, lecturers, administration and staff that we have successfully hacked Manchester.ac.uk networking on June 6th 2023. We have stolen 7TB of data, including confidential personal information from students and staff, research data, medical data, police reports, drug test results, databases, HR documents, finance documents and more.”
On June 9th,the University of Manchester made its initial announcement about the attack, alerting the community to the probable theft of data. Although specific information about the attack was not initially disclosed, it was later uncovered that it was indeed a ransomware incident.
The University of Manchester clarified that the incident is distinct from the recent MOVEit Transfer data theft attacks and the associated data breach at Zellis.
In the world of ransomware attacks, it is customary for malicious actors to first pilfer data before embarking on device encryption. This stolen data serves as a crucial component of their double-extortion tactic, wherein the threat actors leverage the threat of data leakage unless a ransom is promptly fulfilled.
While no specific ransomware group has claimed responsibility for the assault on the University of Manchester, the veracity of their threats may become apparent through the potential publication of data on a designated leak site.
Don’t wait before it’s too late
Having a trusted cyber security company readily available during ransomware attacks proves to be invaluable. It’s important to invest in your cyber security. They will possess the necessary tools to analyse and identify an attack's origin, fortify defences, and promptly neutralise the ransomware's impact. Some ways in which they can help are:
- Risk assessments: Cyber security companies can conduct comprehensive risk assessments to identify vulnerabilities within an organisations network, systems, and processes. This helps in identifying potential entry points for ransomware attacks and implementing appropriate security controls.
- Training and awareness: Cyber security companies can provide tailored training programs to educate employees about common attack vectors, such as phishing emails and malicious attachments. By increasing awareness and promoting good security practices, employees can become the first line of defence against ransom ware attacks.
- Incident response planning: Experts can assist in developing an incident response plan tailored to the organisation's specific needs. This plan outlines the steps to be taken in the event of a ransomware attack, including containment, eradication, and recovery, minimising the impact and downtime.
By engaging a cyber security company, organisations benefit from rapid incident response, enhanced threat intelligence, and tailored strategies to combat evolving cyberthreats. This partnership fosters a proactive security culture and bolsters resilience, enabling organisations to navigate the challenging landscape of ransomware attacks with confidence and mitigate potential damages.


