An ad that appears to be genuine for Amazon within Google search outcomes redirects users to a Microsoft Defender tech support scheme, which subsequently freezes their web browser.
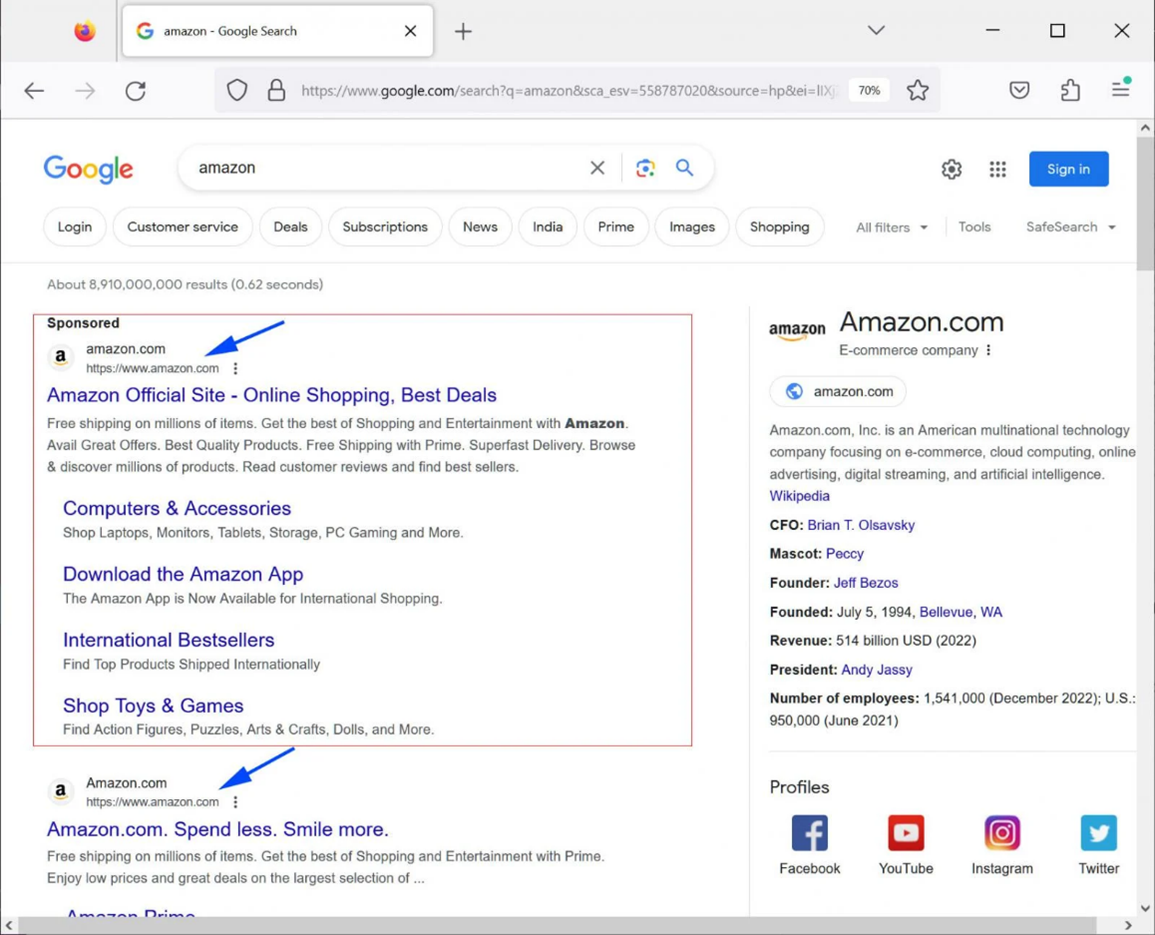
The ad displays Amazon’s genuine URL, mirroring the format seen in the company’s regular search outcomes, as depicted below.
Nonetheless, tapping the Google advertisement will lead the individual to a tech support hoax masquerading as a Microsoft Defender warning, claiming an infection with the ads(exe).finacetrack(2).dll malware.
These tech support deceptions will enter full-screen mode automatically, creating difficulty in exiting the page without ending the Google Chrome process.
Yet, when Chrome is terminated using this method, upon reopening, it will ask users if they want to restore the previously closed tabs, thereby reopening the tech support scam.
In June 2022, a credible-seeming YouTube advertisement was identified, utilizing the platform's web address, and directing users to the identical tech support scam.
The rationale behind Google's allowance of advertisers to mimic URLs from other companies for the purpose of crafting such persuasive ad scams remains uncertain.
Exploitation of Google Ads for Malware distribution
In the last year, Google ads have been extensively misused by malicious actors to disseminate malware, occasionally resulting in ransomware assaults.
The malicious individuals would craft duplicates of authentic websites, substituting the download links with ones that disseminate trojanised applications designed to install malware.
With the increasing number of threats posed by the exploitation of Google advertisements for malware distribution and the subsequent escalation to ransomware attacks, the importance of cyber security services amplifies.
To Sum Up
Through vigilant threat detection, a cyber security team can promptly identify and thwart attempts to replicate legitimate sites for malicious purposes, thereby preventing the installation of harmful software. By actively monitoring and filtering advertisements, they can disrupt the propagation of malicious content and safeguard users from unwittingly interacting with harmful links.
Additionally, a team of cyber security professionals can perform vulnerability assessments, ensuring that websites remain resilient against unauthorised alterations. Their prompt incident response measures provide the means to contain and mitigate the fallout of ransomware attacks, minimising the disruption to businesses and individuals. Through education and training initiatives, these services aim to assist users to discern the tell-tale signs of malevolent activities and respond effectively.


